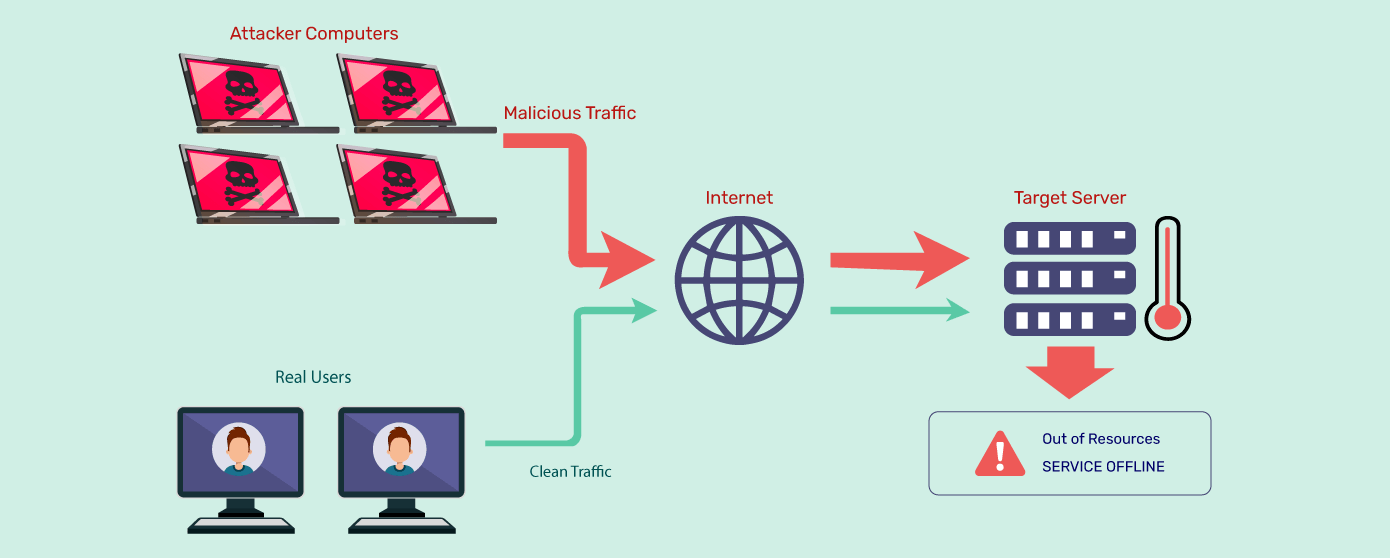
Free Course: Network Programming with Python Course (build a port scanner, mailing client, chat room, DDOS) from freeCodeCamp | Class Central
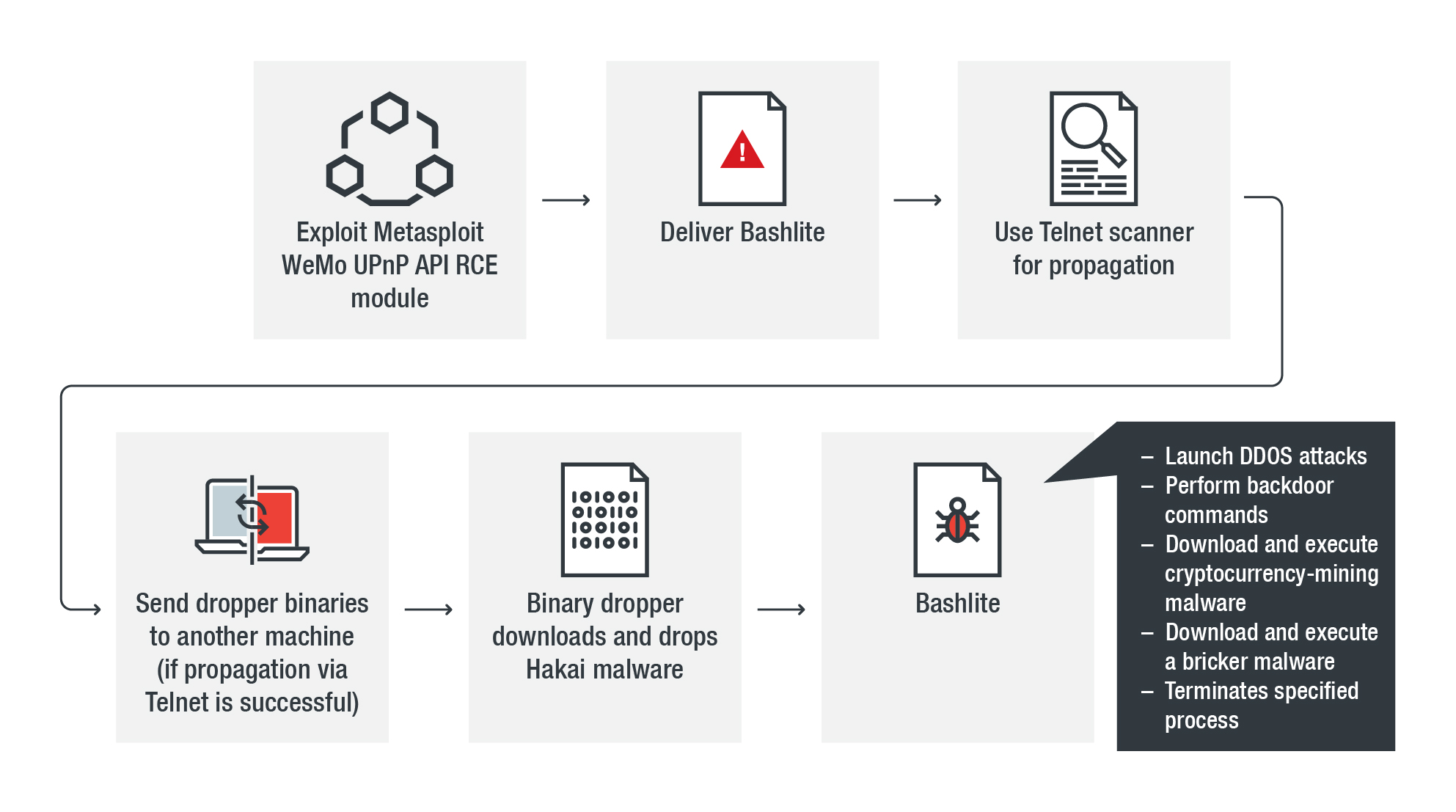
![PDF] Machine Learning Classification of Port Scanning and DDoS Attacks: A Comparative Analysis | Semantic Scholar PDF] Machine Learning Classification of Port Scanning and DDoS Attacks: A Comparative Analysis | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/4c304cfa88cd53cddd7f5547d9728737aa0988c7/2-Figure1-1.png)
PDF] Machine Learning Classification of Port Scanning and DDoS Attacks: A Comparative Analysis | Semantic Scholar

How to Help Protect Dynamic Web Applications Against DDoS Attacks by Using Amazon CloudFront and Amazon Route 53 | AWS Security Blog