How a misconfigured Lotus Domino Server can lead to Disclosure of PII Data of Employees, Configuration Details about the Active Directory, etc | by Aayush Vishnoi | Medium

Ibm Lotus Domino Designer 6 Application Development With Lotus Domino Designer | PDF | Ibm Notes | Databases

Solved: Trellix Support Community - ENS Exploit Prevention - "Suspicious Double File E... - Support Community

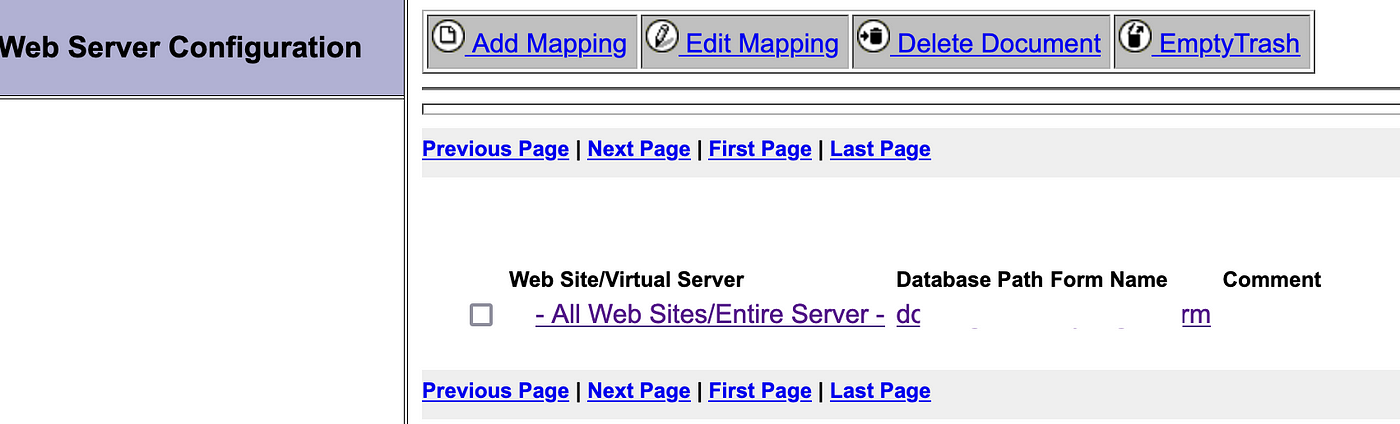
How a misconfigured Lotus Domino Server can lead to Disclosure of PII Data of Employees, Configuration Details about the Active Directory, etc | by Aayush Vishnoi | Medium
CVE-2005-2428-IBM-Lotus-Domino-R8-Password-Hash-Extraction-Exploit/exploit.py at master · schwankner/CVE-2005-2428-IBM-Lotus-Domino -R8-Password-Hash-Extraction-Exploit · GitHub

How a misconfigured Lotus Domino Server can lead to Disclosure of PII Data of Employees, Configuration Details about the Active Directory, etc | by Aayush Vishnoi | Medium

How a misconfigured Lotus Domino Server can lead to Disclosure of PII Data of Employees, Configuration Details about the Active Directory, etc | by Aayush Vishnoi | Medium